Hi Community,
I don’t consider myself a security specialist (or specialist at anything for that matter but a generalist instead). I am currently architecting a Web solution for one of my clients, and they came to me with a requirement “review, assess and rectify security vulnerabilities” on an existing Web application. it’s not what I often do, and the new application will integrate into the existing, so I agreed on helping them with this requirement and in doing so this will help me understand the existing solution. The vulnerabilities I had to address were:
- Remove common IIS/ASP.NET headers
- Enable HTTP Strict Transport Security (HSTS)
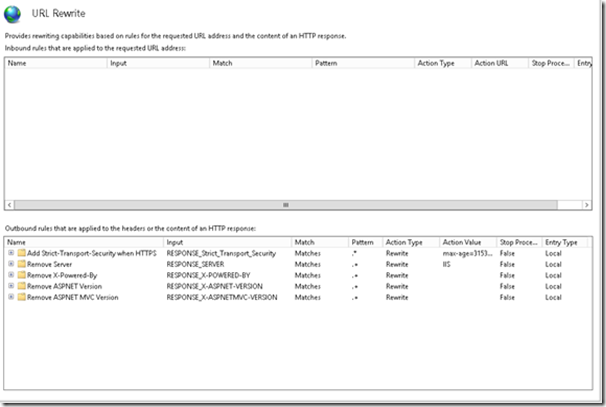
In order to get started, I needed to download the “URL Rewrite” module for IIS, then create a few outbound rules. The resulting web.config file were then checked in to TFS and ready to be used when deploying to a different environment (e.g.: UAT). Below the rules created in IIS, as well as the generated config file with these rules
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<system.webServer>
<rewrite>
<outboundRules>
<rule name="Add Strict-Transport-Security when HTTPS" enabled="true">
<match serverVariable="RESPONSE_Strict_Transport_Security" pattern=".*" />
<conditions>
<add input="{HTTPS}" pattern="on" ignoreCase="true" />
</conditions>
<action type="Rewrite" value="max-age=31536000" />
</rule>
<rule name="Remove Server">
<match serverVariable="RESPONSE_SERVER" pattern=".*" />
<action type="Rewrite" value="IIS" />
</rule>
<rule name="Remove X-Powered-By">
<match serverVariable="RESPONSE_X-POWERED-BY" pattern=".*" />
<action type="Rewrite" />
</rule>
<rule name="Remove ASPNET Version">
<match serverVariable="RESPONSE_X-ASPNET-VERSION" pattern=".*" />
<action type="Rewrite" />
</rule>
<rule name="Remove ASPNET MVC Version">
<match serverVariable="RESPONSE_X-ASPNETMVC-VERSION" pattern=".*" />
<action type="Rewrite" />
</rule>
</outboundRules>
</rewrite>
</system.webServer>
</configuration>
An interesting article on the subject can be found here on MSDN
Regards,
Angel